Gigamon integration
Make security accessible by meshing Gigamon with your network and security services
Supported Products
- GigaVUE
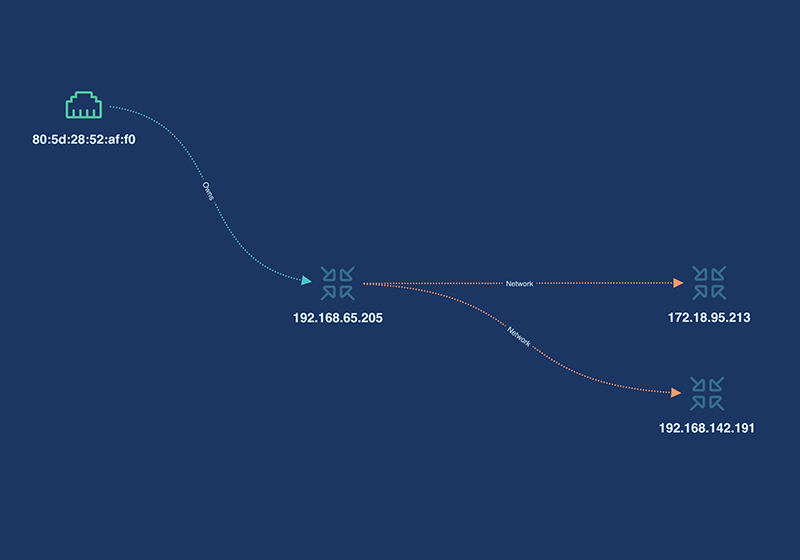
Gigamon traffic data is retrieved by appNovi through API to aggregate network connections between endpoints across the network including hybrid and multi-cloud environments. When Gigamon data is aggregated with other cyber asset data sources users search across all cyber assets to identify those with security control gaps. Saving queries with integrated outcomes provides the ability to automatically identify gaps in security controls and automate remediation through your existing orchestration solution.

Gigamon’s traffic is aggregated alongside other traffic in appNovi for complete visualization of your network connections between cyber assets across your multi and hybrid cloud environments. Understanding cyber asset network connections enable the identification of application components, their owners, and business significance to enable informed risk management and ensure a non-disruptive incident response.
Related Integrations
Azure
ExtraHop
Arista

Fortinet
VMware
Case Studies
Realizing the Potential of XDR
What is XDR? XDR seeks to integrate data from the IT data sources enterprises have: user data, infrastructure configurations, email, network traffic, workloads, and more. By delivering converged data, XDR aims to provide security teams with a richer, more...
Solution Briefs
appNovi Solution Brief
Learn about the appNovi cybersecurity mesh platform for attack surface identification and mapping, vulnerability management, and incident response enablement.
Resources
Explore how appNovi can help you align to CIS controls to mature vulnerability management, attack surface mapping, incident response, and data center migration processes.