What is XDR?
XDR seeks to integrate data from the IT data sources enterprises have: user data, infrastructure configurations, email, network traffic, workloads, and more. By delivering converged data, XDR aims to provide security teams with a richer, more nuanced understanding of their threat landscape, enabling more effective and timely responses.
As we work with enterprise customers we’ve realized that the idealistic scenario of achieving XDR has often been difficult to achieve. Sometimes it’s simply due to the level of effort required to converge data with limited resources. It also seems that XDR has been inappropriately applied by vendors to tools that are unable to deliver enriched security data the technology promises — often due to technical and political reasons. As we work through data convergence with our enterprise customers, we have made several observations that may be helpful to understand common challenges as well as methods to overcome them.
At the end of the day, the more informed the SOC is, the more efficient it is, and the more risk is reduced. Data fuels the SOC – data refinement is necessary to turn the crude data into complete insight to empower security decision-making.
Today’s Challenge: The Best of Breed Dilemma
Modern enterprises face a paradox. On one hand, they’ve invested in best-of-breed tools for specific security functions. On the other hand, these specialized tools often don’t “speak the same language,” resulting in operational blind spots and an incomplete view of the organization’s security posture. SIEMs were meant to resolve this, but they are often data aggregators that have limited enrichment with their compiled logs hidden behind a query language.
Consider a common example. A firewall IDS alert flags an IP address for a log4j vulnerability. While crucial, this single data point is far from sufficient. The IP address might correspond to multiple interfaces, each with its own host, varying CVEs, and owner(s). Without the complete and contextualized view that XDR provides, the security analyst would be left piecing together this complex puzzle to determine which host has the matching CVE, receiving the malicious traffic, and who the owner is of the host, wasting valuable time in the process.
This fragmented approach to security is not just inefficient; it’s risky. Security teams often find themselves swamped with data from different tools, each with its own system for scoring and prioritizing vulnerabilities. The outcome is either an inability to effectively prioritize risk or wasted time on manual analysis with longer MTTR.
A Strong Defense is Predicated on Total Neutrality
As IT and cybersecurity tools proliferate, the need for a unifying layer becomes increasingly evident. That’s why XDR is so alluring to security teams. However, to be effective, XDR solutions need to be vendor-neutral, ensuring a seamless flow of data across all existing tools and platforms. Selectivity only results in additional work for security teams impeded by access and escalations.
Consider a common example enterprise security teams are faced with, especially those that undertake M&A activity. An enterprise uses multiple scanning solutions for application and network vulnerabilities. Each team or child company has its own preferred tool, leading to a dispersed and fragmented vulnerability picture. A truly neutral XDR solution would unify these disparate data streams into a coherent, actionable view. Not just the vulnerabilities, but prevalence across the enterprise, risk to each company, and the network interconnectivity’s influence on the risk.
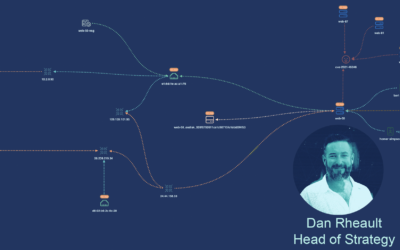
As former security practitioners, this disparate and uneven level of data access inspired our spirit of neutrality in which we operate. As the industry’s first Cybersecurity Mesh Architecture (CSMA) platform, we offer seamless integrations with your existing tech stack to converge and contextualize the data, fulfilling the vision of Cyber Asset Attack Surface Management (CAASM).
Democratization and Action: Beyond Visibility
True cybersecurity resilience goes beyond mere visibility; it requires actionable insights accessible to all relevant parties. In many organizations, alerts and threats require interpretation by Subject Matter Experts (SMEs), which often results in delays due to ticketing and escalation processes. Prolonged responses equate to longer dwell times and increased risk – removing these obstacles would uplevel the SOC.
Consider a common path of an alert in the SOC. An alert often necessitates a domain specialist’s interpretation. This means escalating the ticket to a qualified expert, who prioritizes it alongside many other tasks. This multi-tiered approach can delay response times and introduce the risk of partial or incomplete resolution.
By contrast, a democratized setting removes the need for such escalations. It abstracts the data into a universally understandable format for all security analysts. By democratizing access to essential data, organizations can shorten response times, streamline processes, and enable a more effective incident response.
XDR Today and Into Tomorrow
The initial incarnations of XDR were often tailor-made to fit particular customer bases. While this strategy has its merits, it overlooks an essential truth: no two customers are alike. XDR platforms must serve as neutral arbitrators, integrating data across a plethora of tools and services. Only then can organizations truly uplevel their extended detection and response capabilities.
We sat in the seats of the SOC. We faced the same problems security teams face today. And now we’re solving them – see how.