ExtraHop integration
Prioritize contextually exploitable vulnerabilities and their business importance
When you don’t have to choose between protecting your business and moving it forward, that’s security not compromised. Learn more at www.extrahop.com.
Supported Products
- ExtraHop Reveal(x) 360

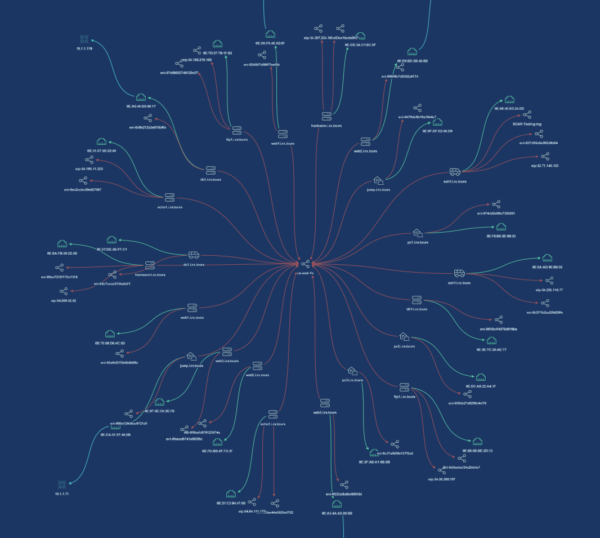
Integrate ExtraHop with the rest of your tech stack to gain an authoritative source of data that delivers immediate asset context to security teams. Understand assets, their owners, their importance to the business, and avoid unnecessary ticket escalations while reducing mean time to resolution (MTTR).
Related Integrations
Azure
Gigamon
Arista

Fortinet
VMware
Case Studies
Realizing the Potential of XDR
What is XDR? XDR seeks to integrate data from the IT data sources enterprises have: user data, infrastructure configurations, email, network traffic, workloads, and more. By delivering converged data, XDR aims to provide security teams with a richer, more...
Solution Briefs
appNovi Solution Brief
Learn about the appNovi cybersecurity mesh platform for attack surface identification and mapping, vulnerability management, and incident response enablement.
Resources
Explore how appNovi can help you align to CIS controls to mature vulnerability management, attack surface mapping, incident response, and data center migration processes.