Tenable integration
Mesh your network and security services to align to CIS controls 1 and 2 and implement business-specific risk prioritization
Tenable® is the Cyber Exposure company. Approximately 40,000 organizations around the globe rely on Tenable to understand and reduce cyber risk. As the creator of Nessus®, Tenable extended its expertise in vulnerabilities to deliver the world’s first platform to see and secure any digital asset on any computing platform. Tenable customers include approximately 60 percent of the Fortune 500, approximately 40 percent of the Global 2000, and large government agencies. Learn more at tenable.com.
Supported integrations
- Tenable.sc
- Tenable.io
appNovi integrates with Tenable solutions to retrieve assets identified through scan events and where agents are installed. Tenable IT asset data is aggregated with other IT asset data sources to provide a complete repository of your enterprise’s infrastructure and software. This data can then be searched to add assets with agents or inclusion in scans as discovered assets to address security control gaps.
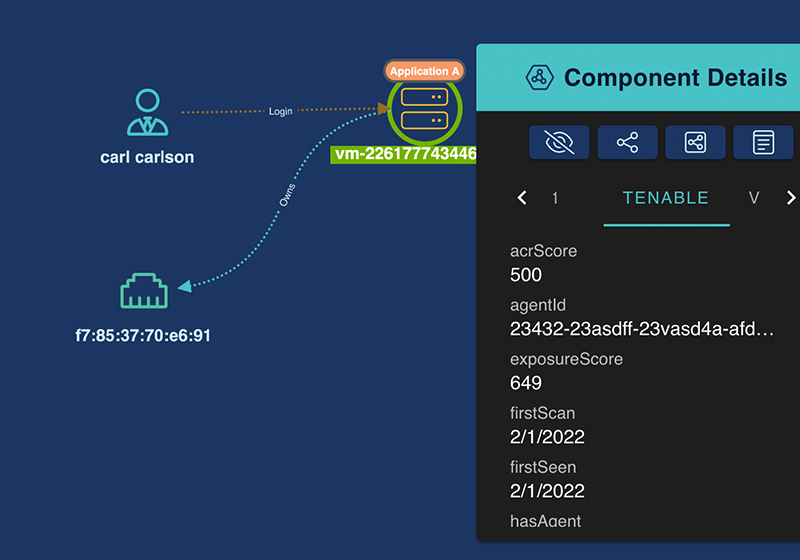
When contextually converged with other data sources such as NetFlow or vulnerability data, appNovi analyzes your network’s infrastructure and/or the contextual exposure for exploitation to identify the cyber asset attack surface..
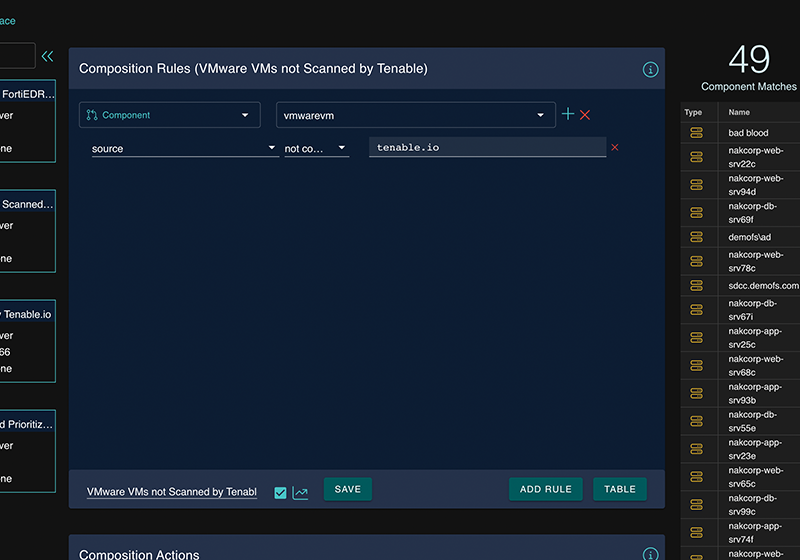
appNovi integrates with Tenable solutions to retrieve asset, vulnerability, and agent status data to identify control gaps in asset management and agent coverage. appNovi contextually converges and aggregates Tenable data with other data sources to analyze network assets’ exposure, identify the cyber asset attack surface, and visualize security events and network connections for more efficient and non-disruptive incident response.
Related Integrations

Tanium
Cisco
Rapid7
Qualys
Fortinet

SentinelOne
Case Studies
Developing a business-specific risk reduction plan with security data visualization
Leveraging cybersecurity mesh to implement business-specific vulnerability management
Solution Briefs
appNovi Solution Brief
Learn about the appNovi cybersecurity mesh platform for attack surface identification and mapping, vulnerability management, and incident response enablement.
Resources
Explore how appNovi can help you align to CIS controls to mature vulnerability management, attack surface mapping, incident response, and data center migration processes.