Tanium integration
Identify security control gaps in endpoint agents and orchestrate remediation

Supported Products
- Tanium Cloud Platform
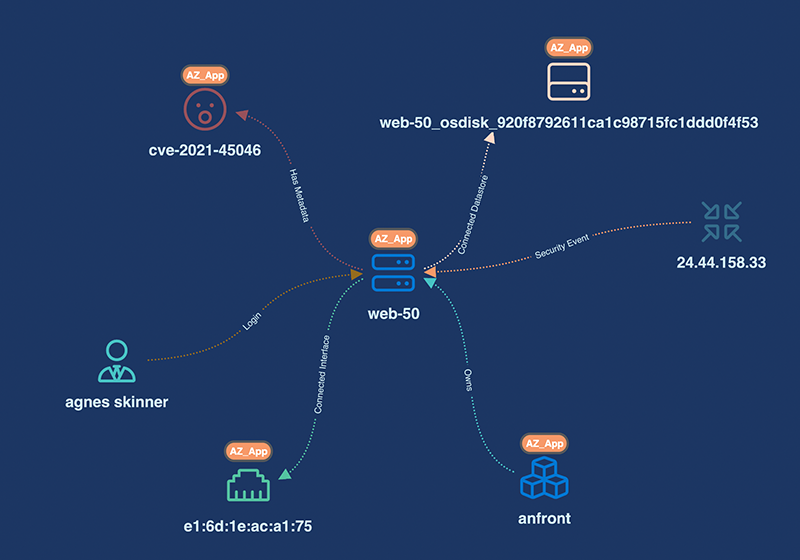
Aggregate your IT assets and software monitored by Tanium EDR agents alongside the rest of your IT asset data sources in appNovi to establish and maintain a single source of truth for all IT assets across the multi and hybrid cloud network. Search cross vendor-created and appNovi enriched metadata to define highly targeted searches to define security control gaps in your IT assets and trigger remediation solutions.

Related Integrations

SentinelOne
ExtraHop
Rapid7
Panther
Fortinet
Crowdstrike
Case Studies
Developing a business-specific risk reduction plan with security data visualization
Leveraging cybersecurity mesh to implement business-specific vulnerability management
Solution Briefs
appNovi Solution Brief
Learn about the appNovi cybersecurity mesh platform for attack surface identification and mapping, vulnerability management, and incident response enablement.
Resources
Explore how appNovi can help you align to CIS controls to mature vulnerability management, attack surface mapping, incident response, and data center migration processes.